Contents
Cloud Security
Tunnel Vision Design partners with cloud infrastructure and security provider Cloudflare to protect from malicious attacks and cache assets for every client’s website. Recently, Cloudflare announced that it had mitigated one of the largest distributed denial of service attacks (DDoS) in history. We believe security isn’t something that should cost you extra, so we include DDoS prevention, bot attack mitigation, and WordPress firewall security protection with every hosting plan.
Web infrastructure and website security company Cloudflare on Thursday disclosed that it mitigated the largest ever volumetric distributed denial of service (DDoS) attack recorded to date.
The attack, launched via a Mirai botnet, is said to have targeted an unnamed customer in the financial industry last month. “Within seconds, the botnet bombarded the Cloudflare edge with over 330 million attack requests,” the company noted, at one point reaching a record high of 17.2 million requests-per-second (rps), making it three times bigger than previously reported HTTP DDoS attacks.
https://thehackernews.com/2021/08/cloudflare-mitigated-one-of-largest.html
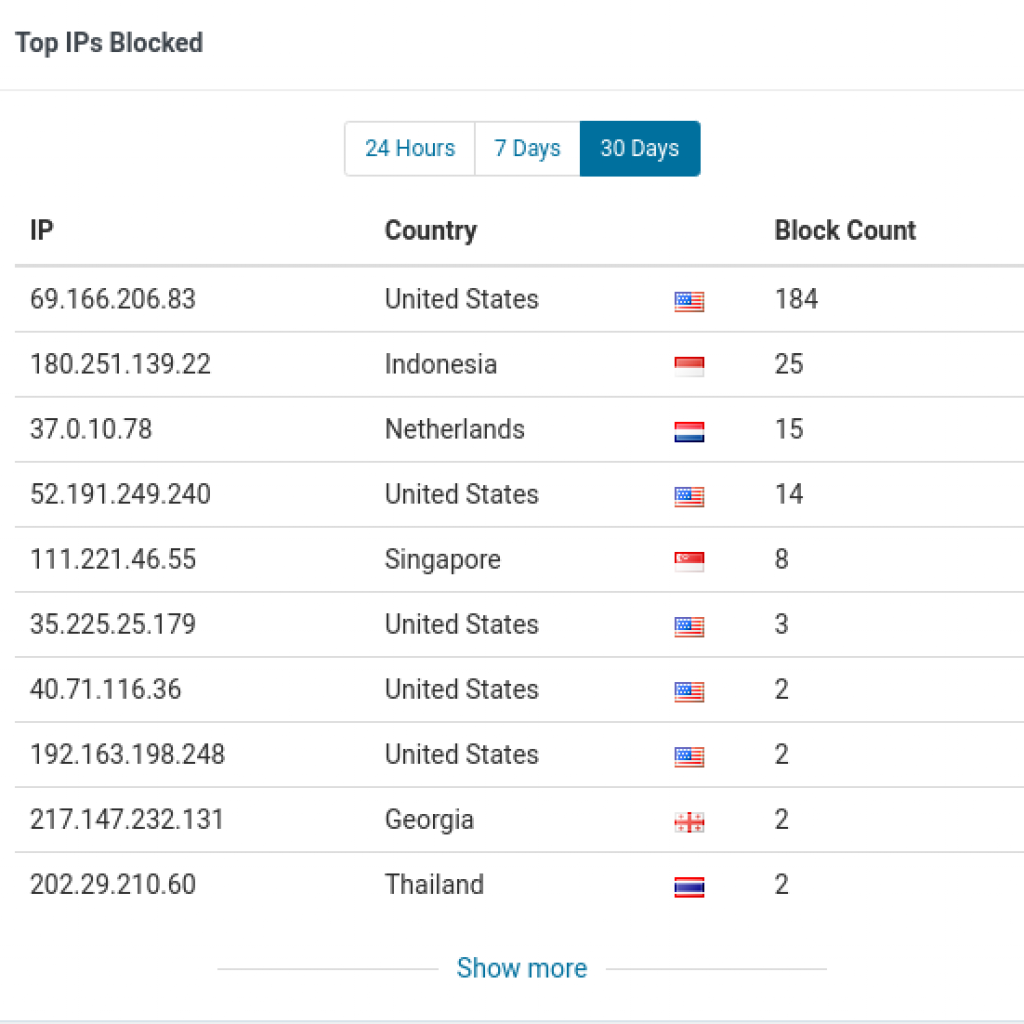
Here’s an example of some of the statistics and visualizations we have access to about each of our sites. We can see at a glance where the majority of malicious attacks and threats originate–then we can take action if necessary.


Firewall Technology
Our exclusive firewall technology automates many security tasks that previously required a full-time IT security staff. Items such as failed administration logins, brute force password attacks, insecure site probes, and rapid accessing of pages will result in automatic blocking of the computer’s IP address. Our systems are working 24/7 to keep your site and data as safe as possible from malicious attacks. We won’t hesitate to permanently block foreign hackers and users with bad intentions from accessing your valuable site.

Secure Hosting
Our preferred hosting provider protects your data, backups, and web traffic. All data on our host’s servers are encrypted at rest and in transit so you can rest easy. The host utilizes an intrusion detection system to automatically alert if there are attempts to infiltrate the network with malicious attacks. The data center environment undergoes an SSAE-18 examination at least annually. SSAE-18 ensures high standards of data compliance and evaluation of risk and it also requires companies to apply the same risk assessment standards to their vendors. It is considered one of the most important data center compliance standards available today. It covers financial reporting, data availability, privacy, integrity, confidentiality, and internal security controls.
Our hosts pledge that all computing equipment is located in a physically secure facility, where electronic access controls are used to prevent unauthorized access. They also conduct background screenings of all personnel that have access to any critical infrastructure.
Encrypted Traffic (SSL/TLS)
Security professionals recommend all web traffic be encrypted yet an estimated 20-25% of sites still aren’t using SSL or TLS to encrypt the data that passes between a server and a user’s computer. This can leak confidential information such as emails, logins, passwords, and credit cards if the traffic is intercepted along the way.
Google in the recent past started penalizing sites that aren’t encrypting traffic, so even if your site doesn’t contain any privileged information it is still vital to be secure from malicious attacks. At Tunnel Vision Design, we don’t believe you should be charged extra for an SSL certificate, yet many of our competitors are charging $250 a year or more above any costs.
System / Plugin Updates
The most important way to keep any site safe is making sure the software is up to date. For any content management system website, the number one reason for getting hacked is out of date plugins or system software. If you get hacked, your business may have to spend tens of thousands cleaning up your site and repairing any damage due to search engine penalties.
Most of our hosting plans come with included maintenance hours where we handle your security updates for no extra charge. You won’t have to worry about choosing between running an out of date site or paying a large, unexpected bill to stay secure.
Contact us for a Free Consultation
If you are concerned about your site’s security and are ready to move to top notch service and protection, set up an appointment or send us an email and we can help you get started on the road to success and safety.
“While the majority of attacks are small and short, we continue to see these types of volumetric attacks emerging more often,” Cloudflare said. “It’s important to note that these volumetric short burst attacks can be especially dangerous for legacy DDoS protection systems or organizations without active, always-on cloud-based protection.”
https://thehackernews.com/2021/08/cloudflare-mitigated-one-of-largest.html
References
https://blog.cloudflare.com/cloudflare-thwarts-17-2m-rps-ddos-attack-the-largest-ever-reported/
https://www.vxchnge.com/blog/data-center-ssae-18-compliance
https://thehackernews.com/2021/08/cloudflare-mitigated-one-of-largest.html